Tag: Bytecode
-

The Hidden Vulnerabilities of Bytecode and JIT in Modern Software
In the ever-evolving world of software development, security continues to be a paramount concern. Recent developments have brought attention to vulnerabilities within bytecode and Just-In-Time (JIT) compilation systems, with Factorio’s Lua implementation serving as a notable example. Bytecode and JIT, although designed to optimize performance, introduce complex security challenges that can lead to serious exploits…
-
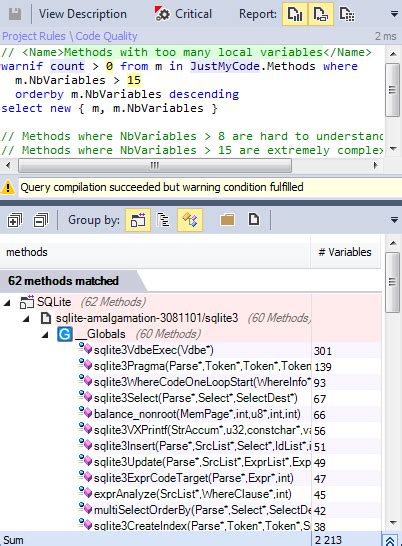
Exploring the Efficiency of SQLite’s Bytecode Approach
The design architecture of SQLite utilizes a bytecode approach rather than a traditional Abstract Syntax Tree (AST) walking technique. This strategic choice by SQLite’s creators resonates with a broader paradigm in computer science where bytecode virtual machines (VMs) underpin numerous software systems to enhance portability, modularity, and performance. The choice of a bytecode mechanism over…
