Tag: SSH
-
Substituir Sudo por SSH: Segurança ou Desperdício de Esforço?
Recentemente, uma discussão fervorosa emergiu em torno da ideia de utilizar SSH como uma substituição ao sudo. Essa mudança, embora intrigante, levanta diversas questões sobre a segurança e a complexidade do sistema. Entender a lógica por trás disso pode nos ajudar a decidir se realmente vale a pena considerar essa abordagem ou se estamos simplesmente…
-
Revamping Root Access: Could SSH Replace Sudo?
Root access in Unix-like systems has always been a hot topic of debate among system administrators and security professionals. Traditionally, the ‘sudo’ command has been the go-to tool for gaining superuser permissions without logging in as root. However, a recent thought-provoking experiment suggests using SSH (Secure Shell) as an alternative method to obtain root-level permissions.…
-
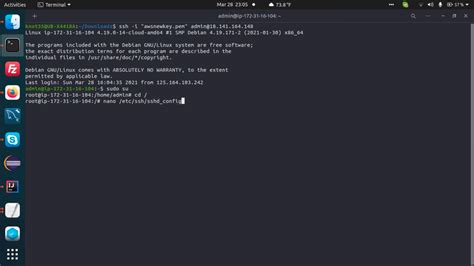
Navigating the Murky Waters of Off-Path TCP Hijacking in NAT-Enabled Wi-Fi Networks: Are We Really Safe?
In the realm of cybersecurity, the phrase ‘off-path TCP hijacking in NAT-enabled Wi-Fi networks’ might sound like a plot straight out of a techno-thriller. However, it is a very real concern, particularly for users who frequent public Wi-Fi hotspots. Despite the advances in security technology, this old yet potent form of attack reminds us that…
-
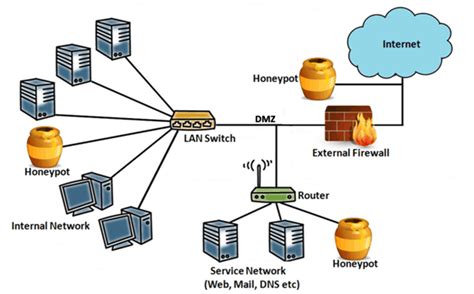
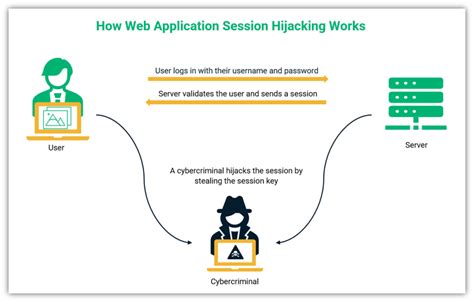
La Realidad Inquietante de los Honeypots SSH: Explorando los Peligros de Exponer Puertos al Internet
Exponer puertos en el Internet es uno de los mayores riesgos para cualquier administrador de sistemas. Recientemente, un honeypot SSH, un señuelo digital diseñado para atraer a potenciales atacantes, demostró la inquietante cantidad de intentos de acceso no autorizados que pueden ocurrir en tan solo 30 días. La cantidad de intentos de hacking documentados no…
-
30 Days Behind Enemy Lines: Running An SSH Honeypot and What I Learned
Operating an SSH honeypot for a month is a revealing yet sobering endeavor. By essentially setting a trap for cyber attackers, you can gain firsthand insight about the myriad of threats your Linux systems could potentially face when ports are exposed to the Internet. This deep dive helps underscore the immense value of cybersecurity protocols…
-
Revolução nos Dispositivos Móveis: Como Usar VSCode e Terminal em Qualquer Dispositivo iOS
A tecnologia não para de evoluir e com ela, nossas opções para trabalhar de forma mais eficiente e portátil. Hoje, quero abordar uma mudança significativa no uso de dispositivos móveis para desenvolvedores: rodar VSCode e terminal em qualquer dispositivo iOS. A partir de soluções como o Blink e integrações com Mosh e Wireguard, o iPad…
-

Unleashing Developer Potential: Running VSCode and Terminal on iOS Devices
Developers have long sought ways to maximize the utility of their devices, and the latest breakthrough allowing users to run Visual Studio Code (VSCode) and terminal on any iOS device marks an exciting development in the tech landscape. The power of the iPad continues to grow, with some arguing that it now boasts capabilities comparable…
-

Is Tmux a Must-Have Tool for Developers?
The world of software development is ever-evolving, and one tool that has become indispensable for many developers is Tmux. For those unfamiliar, Tmux is a terminal multiplexer, which essentially means it allows multiple terminal sessions to be accessed and controlled simultaneously from a single screen. This is especially vital for developers who SSH into servers…
-

Tmux: Ein Muss für Serveradministration und Remote-Workflows
In einer Welt, in der Remote-Arbeit und dezentrale Teams immer mehr an Bedeutung gewinnen, ist es wichtig, Werkzeuge zu haben, die diesen Arbeitsstil unterstützen. Ein solches Werkzeug, das sich in den letzten Jahren als unverzichtbar erwiesen hat, ist Tmux. Tmux ermöglicht es Benutzern, mehrere Terminal-Sitzungen innerhalb eines einzigen Fensters zu verwalten. Dies ist besonders nützlich…
-
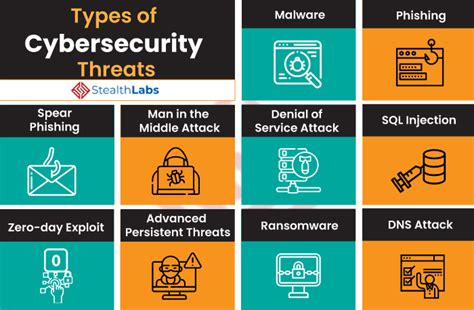
Securing Your Server Online: Common Attacks and Defense Strategies
In the realm of cybersecurity, the moment a server goes online, it becomes a target for malicious entities seeking vulnerabilities to exploit. The comments from tech enthusiasts reveal the harsh reality of the digital landscape, where even a brief exposure to the internet can result in relentless attacks. One prevalent defense mechanism discussed is the…
